Trending
North Korean Hackers Targeting Cyber Security Researchers With Fake Website & Social Media: Google

NEW DELHI: Google announced in January 2020 that cyber criminals have been targeting IT security researchers all over the world. According to the most recent update from Google’s Threat Analysis Group (TAG), a hacking group sponsored by the North Korean government is now threatening security researchers with bogus social media accounts.
They’ve also set up a phoney cyber security firm named SecuriElite, based in Turkey, and using its website to recruit security experts.
According to TAG’s Adam Weidemann, this company allegedly provides aggressive security services such as “pentests, software security reviews, and exploits.” TAG’s team flagged the campaign as early as January 2021, and the website went live on March 17.
How Did Researchers Get Attacked by Hackers?
Google researchers wrote in a blog post published on Wednesday that the attackers used fake accounts and websites to fool naive users. When they clicked on the connection, a browser exploit was immediately launched.
Google discovered eight Twitter accounts and seven LinkedIn profiles in total. To interact with researchers and gain confidence, a research blog and various fake profiles on social media sites such as Twitter, Telegram, LinkedIn, Keybase, and Discord were developed. They then used a trojanized Visual Studio Project to instal a Windows backdoor.
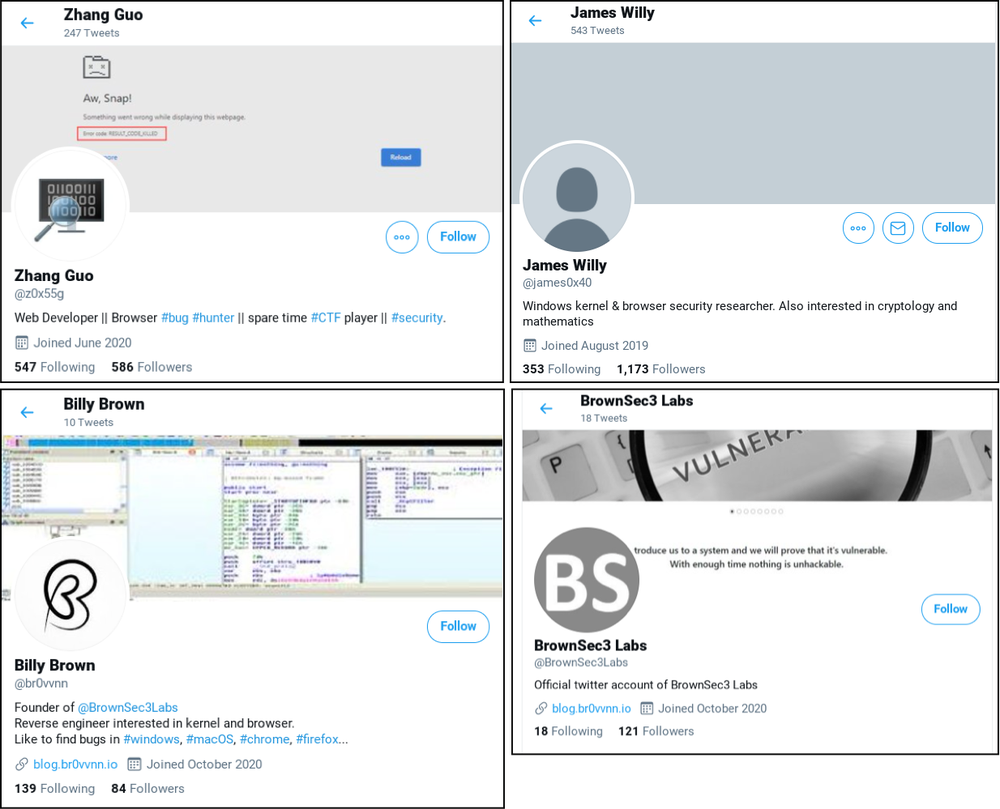
All fake accounts have been disabled.
According to Google, the latest initiative and the LinkedIn and Twitter accounts associated with it were registered, and all of the accounts were disabled as a result.
Human resources staff and vulnerability analysts at various security companies, such as Trend Macro, which is simply a parody of Trend Micro, seemed to be behind the accounts.
Some of the profiles were of people pretending to be the CEO of a fictitious Turkish company. Both of the accounts have been suspended at this time. To prevent users from accessing the fake website by accident, Google has added the link to its Safebrowsing blocklist.
Follow The420.in on Facebook, Twitter, LinkedIn, Instagram, YouTube & Telegram














